CopyFail
The cyber world has been buzzing about the Copyfail exploit. What a fantastic time to be a linux user! (and an even better time to be learning pentesting:D).
What exactly is Copyfail? Essentially, it’s a bug in the Linux OS that lets a low privileged user obtain root privileges through that bug without any crazy privilege escalation.
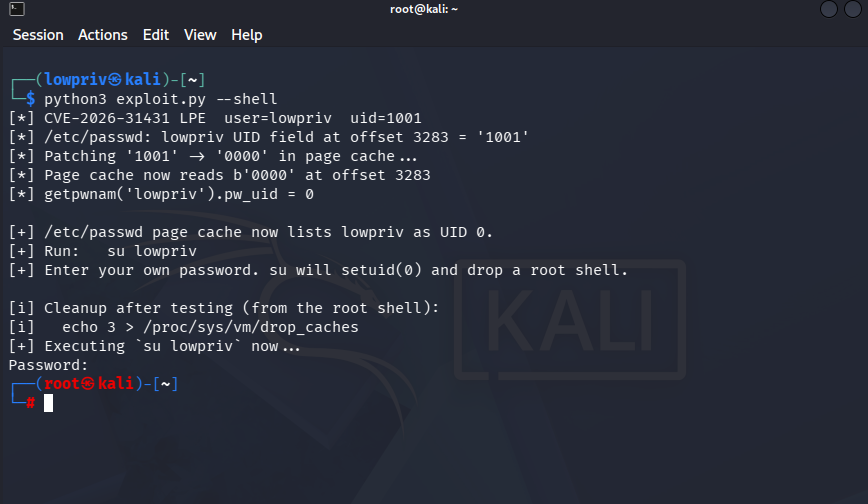
Well, how exactly does it work? Linux has a specific feature for encryption/decryption, but it’s had a flaw since 2017 which was just recently discovered. A simple 4 byte change in the RAM can trick the OS into giving any user root access. Pretty scary.
The crazy part, this affects almost every Linux distro/VM running the kernal since 2017. The only way to mitigate it is to patch your system now!
Here’s a short demonstration of how it works.
NOTE: This was tested on my own personal virtual machine. It’s illegal to run authorized scripts on any machine that isn’t yours
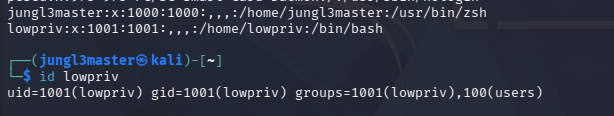
I started off by installing a fresh install of Kali from an installer from last month (March 2026). I added a new user and gave it basic privileges.
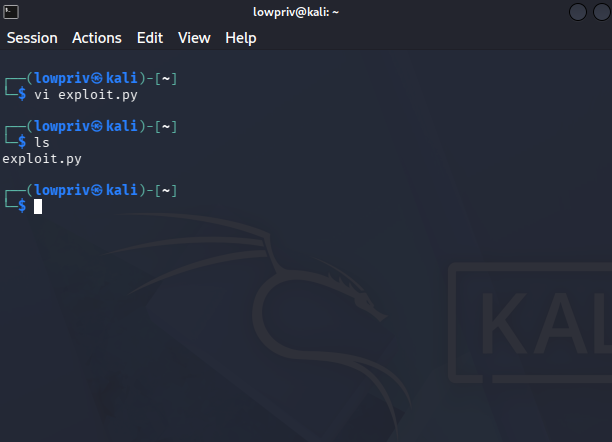
I copied the exploit into a python file ran it.
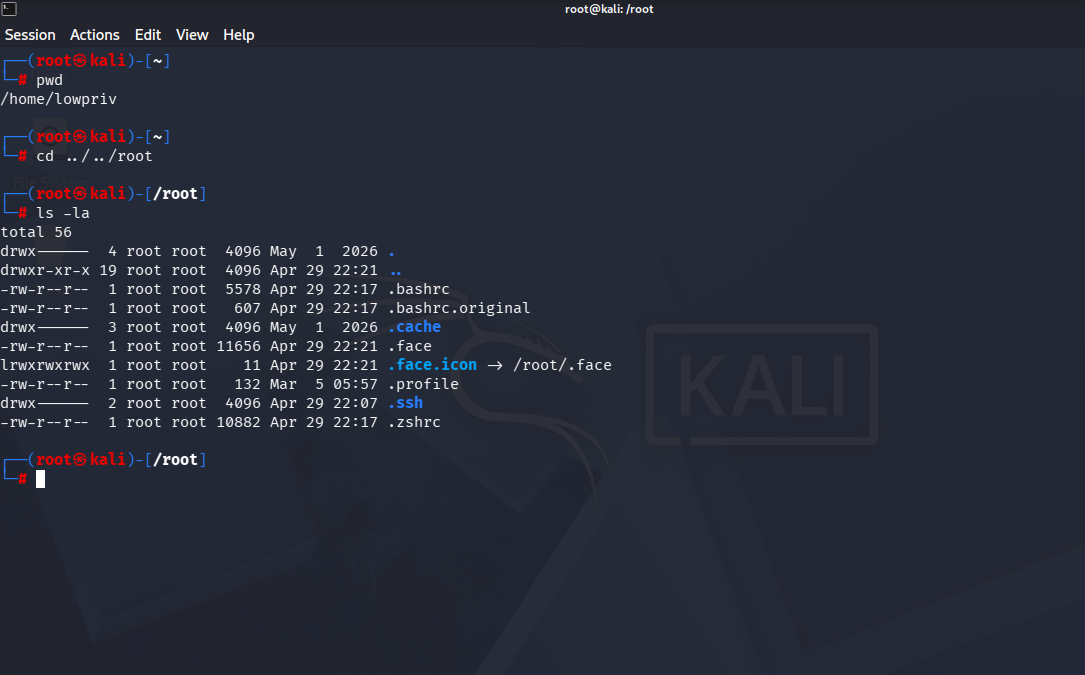
And just like that, I was able to gain root access, just from a simple python script.
This is a very serious issue, as any attacker who even sets foot into your machine can gain complete access in a matter of seconds.
What should you do?
- Update your Linux kernel as soon as patches are available
- If you can't patch yet, block the crypto feature being abused (AF_ALG sockets)
- Check your logs for suspicious activity
Most major Linux distributions have already released patched kernels. You can update your system without needing to handle raw patch files manually.
- Ubuntu / Debian / Mint:
sudo apt update
sudo apt upgrade linux-image-generic
sudo reboot